NEXT-GENERATION FIREWALL
Our next-generation firewalls secure your business with a prevention-focused architecture and integrated innovations that are easy to deploy and use. Now, you can accelerate growth and eliminate risks at the same time.
Our next-generation firewalls are available as physical appliances, virtualized appliances and cloud-delivered service, all managed consistently with Panorama.
- Harness shared intelligence to prevent successful attacks
Palo Alto Networks® next-generation firewalls detect known and unknown threats, including in encrypted traffic, using intelligence generated across many thousands of customer deployments. That means they reduce risks and prevent a broad range of attacks.
- Automate to save time and focus on what matters most
With our next-generation firewalls, you can quickly create security rules that mirror business policy, are easy to maintain and adapt to your dynamic environment. They reduce response times with automated policy-based actions, and you can automate workflows via integration with administrative tools, such as ticketing services, or any system with a RESTful API.
- Leverage innovations that help you adapt
Our next-generation firewalls give you access to the latest innovations of Palo Alto Networks Security Operating Platform.
Products :
 PA-7000 Series Perfect blend of power, intelligence, simplicity and versatility for enterprise and service provider deployments |
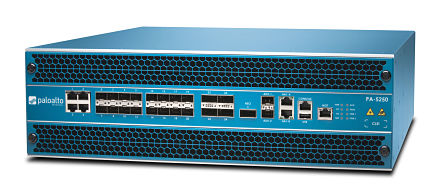
PA-5200 Series No-compromise security and high-performance versatility for data centers and service providers |
PA-5000 Series High-performance with one consistent architecture for data center deployments |
PA-3200 Series Predictable performance and broad threat coverage for the internet edge |
PA-3000 Series Multi-gigabit throughput to prevent attacks on the internet edge |
 PA-800 Series Rock-solid security for the branch and midsize business |
PA-500 Consistent architecture for a broad range of small-business applications |  PA-220R Ruggedized form factor for industrial applications |
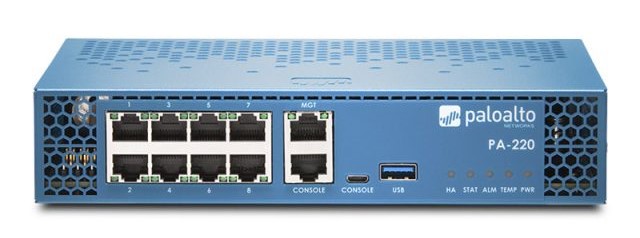
PA-220 Small form factor with the power to prevent network threats |  PA-200 Next-generation firewall in a small footprint |
CLOUD SECURITY
Redlock
RedLock is a critical element of the Palo Alto Networks Security Operating Platform, enabling you to benefit from the industry’s most complete offering for public cloud security. Our other cloud products allow you to:
- Protect and segment cloud workloads
- Adopt advanced host-based protection
2. Aperture
Secure the business-critical data within your SaaS applications.
- Risk discovery and deep visibility
Aperture provides complete visibility across all user and data activity, along with detailed analysis that helps you transition from speculation to certainty about what’s happening at any given point in time.
- Data leak prevention and compliance
Data within enterprise-enabled cloud applications may not be visible to an organization’s network perimeter. Aperture can connect directly to enterprise SaaS applications to provide:
-Data classification and monitoring
-Data Loss Prevention (DLP) capabilities
-User activity tracking for anomalies
-Known and unknown malware prevention
-Detailed risk and usage reporting
- Advanced threat prevention
You can keep threats from spreading through the sanctioned SaaS applications, preventing a new insertion point for malware. New malware discovered by Aperture is shared with the rest of the Security Operating Platform, strengthening your overall security posture.
3. VM-Series
The VM-Series offers a unique combination of visibility, control over your applications and data, and protection against both known and unknown threats. The result is an unprecedented level of security for critical deployments in private and public clouds. Specifically, the VM-Series gives you the ability to:
- Protect mission-critical applications and data
- Block lateral movement of cyberthreats
- Automate security so it keeps pace with your business
ENDPOINT PROTECTION
TRAPS
Protect endpoints from malware, exploits and ransomware. Traps™ advanced endpoint protection stops threats on the endpoint and coordinates enforcement with cloud and network security to prevent successful cyberattacks.
- Simple cloud-based management
With the Traps management service, a cloud-based endpoint security service, you save the time and cost of having to build out your own global security infrastructure. Deployment is simple and fast, requiring no server licenses, databases or other infrastructure to get started.
- Intuitive user experience
Traps provides an intuitive interface that makes it easy to manage policies and events, and accelerate incident response – helping to minimize the operational challenges associated with protecting your endpoints. From the Traps management service web console, you can manage the endpoint security policy, review security events as they occur, and perform additional analysis of associated logs.
- Lightweight, non-disruptive agent
The Traps agent enforces your security policy on the endpoint and reports when it detects a threat. The Traps endpoint agent consists of various drivers and services yet requires minimal memory and CPU usage to ensure a non-disruptive user experience. Following its deployment, system administrators have complete control over all Traps agents in the environment through the Traps management service.
Contact Us